On August 16, 2000, Democrats.com proudly presented the first annual Ken Starr Awards, better known as The Kennys.
The presentation was part of our kickoff "Hush-In on Privacy" at the Democratic Convention in Los Angeles.
The Kennys are inspired by Special Prosecutor Ken Starr, who would stop at nothing in his prosecutorial zeal to "get" President Clinton. In Ken Starr's right-wing view, you have no rights.
Bad Kennys were awarded to the worst violators of our privacy rights, while Good Kennys were awarded to champions of privacy.
Our right to privacy is in greater danger than ever, thanks to advances in technology including the Internet. Worse yet, some bureaucrats, companies, and conservative ideologues actually believe that we have no right to privacy.
While the issues are serious, The Kennys are fun because Ken Starr deserves to go down in history as a joke. After spending 5 years and $60 million investigating every detail of President Clinton's life, Starr failed spectacularly - just like cartoon legend Elmer Fudd, to whom Starr bears a striking resemblance.
Bad Kennys
Bad Kenny Descriptions
FBI. The "T-Rex Kenny" emerges from the forests of darkness to go to FBI, proud creator of the Internet wiretapping system "Carnivore". Why do they call it "Carnivore"? Because it's the next evolution of its predecessor, "Omnivore". Omnivore swallowed up everything --jokes, recipes, viruses, beanie-baby auctions -- you name it! It filled the FBI's hungry belly with too much data -- producing a government-sized stomach-ache. But alas, this did not help the FBI spot those needle-in-the-haystack threats to our National Security. So Carnivore lets the fattening stuff go by, and just swallows "the meat". Privacy advocates are in hot pursuit, but the FBI's Carnivore is still a ravenous dinosaur chomping down our right to privacy, so they are the winners of our T-Rex Kenny Award.
Intel: The "Inside-Job-Kenny" goes to Intel. As the supplier of the microprocessor for most of America's personal computers, Intel is proud to plaster its "Intel Inside" sticker on the outsides of our computers. But it isn't eager to reveal what its chips are really doing inside. When it was discovered that each Intel chip was shipped with a unique serial number making it possible for web sites to identify and track every Intel customer, Intel tried to argue that this was no big deal. Privacy advocates launched the "Big Brother Inside" campaign, which ultimately forced Intel to change its ways. But Intel has abused our trust, so they are the winners of our Inside Job Kenny award.
Doubleclick: The "Doublecross Kenny" goes to Doubleclick, the largest Internet advertising solutions company. Doubleclick is the company that clogs up our browsers with all of those annoying banner ads like "catch the monkey". Well, it turns out that Doubleclick doesn't just distract us - it also tracks our online behavior. In the past, people didn't complain much about this spying because it was supposed to be anonymous. But then Doubleclick bought a company called Abacus, which owns a massive file of names, addresses, and stuff you buy offline. Privacy advocates forced Doubleclick to back off - for now at least. But Doubleclick tried to sell out our privacy, so they are the winners of our Doublecross Kenny award.
Real Networks: The "Reality Bites Kenny" goes to Real Networks, the largest audio and video streaming technology company. Re Networks produces nifty software like RealJukebox, which you can load onto your computer to listen to music over the Internet. Real Networks also hosts progressive radio programs like Democracy Now and Jim Hightower on its Webactive site. Unfortunately, some senseless programmers at Real Networks turned RealJukebox into a spy system to send back reports on which songs its customers were playing - until privacy advocates caught them in the act. Real Networks has learned that consumers take privacy seriously, so they are the winners of our Reality Bites Kenny award.
Toysmart: The "Big Bad Wolf Kenny" goes to Toysmart, an Internet toy store that urges parents to "click on their child's potential." Toysmart seems like the kind of place where kids are safe, and Toysmart was proud of its privacy policy, which promised never to sell information about its little customers. But when sales remained kid-sized and Toysmart faced bankruptcy, they changed their tune and tried to sell their list of children. Privacy advocates challenged this sale and ultimately stopped it. But Toysmart has bared its long teeth, so they are the winners of our Big Bad Wolf Kenny award.
Republican Party: The "Terminator Kenny" goes to the Republican Party, the party that puts profits before people regardless of the issue. Privacy abuses like those of our Kenny winners have made headlines and prompted citizens to demand tougher laws to protect privacy. But when Democrats like Representatives Louise Slaughter, Jay Inslee, and Ed Markey have drafted laws that would make a difference, Republicans like Phil Gramm, Jim Jeffords, Tom DeLay, and Bill McCollum have led their fellow Republicans in successful efforts to stop those laws dead. The Republican Party has taken its stand, and it stands solidly against passing laws to protect privacy, with privacy abusers rather than the people, so the Republican Party is the winner of our Terminator Kenny award.
Ken Starr: The "Elmer Fudd Kenny" goes to Ken Starr himself, the hero of our Ken Starr Awards. Ken Starr likes to pose as the paragon of virtue, a modern-day moral saint waging a crusade against our corrupt morals. But something about the Clintons makes Starr go wild with rage, like Elmer Fudd pursuing Buggs Bunny. Starr spent 6 years and $60 million dollars trying to "get" Bill and Hillary Clinton, using the almost unlimited powers of the independent prosecutor. He fired a lot of shots, but in the end the shots backfired and brought about the end of the independent counsel law. Starr's failed bumbling crusade also made Starr a national joke, so Ken Starr is the winner of our Elmer Fudd Kenny award.
Good Kennys
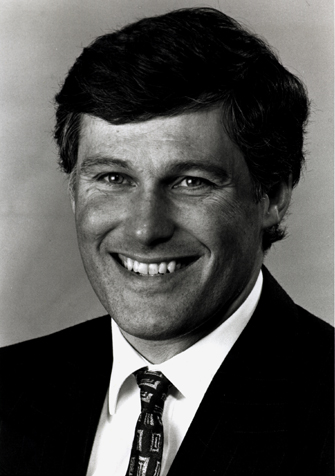
 | Rep. Louise Slaughter is a leader in Congress on privacy. As a microbiologist, Congresswoman Slaughter understands the critical importance of privacy in our health care system. Throughout her career, she has fought to protect the fundamental right of privacy that is at the core of the Supreme Court's 1973 decision in Roe v. Wade that recognized a woman's right to choose. More recently, Louise has led the fight to protect Americans against abuse of genetic profiles, so no one loses their job or their insurance as a result of a confidential diagnostic test. |
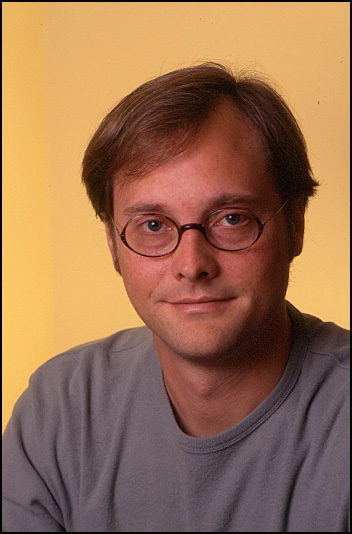
 | Representative Jay Inslee of Washington State's 1st district is also a leader in Congress on privacy. Congressman Inslee gave a masterful address to the Convention yesterday afternoon that was the first mention in the big hall of privacy, an issue that we think Americans are anxious to hear more about. He has worked hard in the Congress to protect the privacy of financial records. He has fought to create a right for consumers to opt out of the use of their private information for marketing purposes. If we get a Democratic majority in Congress this November much of what Congressman Inslee has been fighting for on our behalf will finally become law. |
 | Christine Gregoire is the Attorney General of the State of Washington, which is home to some of the largest Internet companies. General Gregoire is the state's leading consumer advocate, and she has led the fight to protect the privacy of the citizens of her home state. In addition, General Gregoire serves as chair of the National Association of Attorneys General, and has led the fight nationally to protect the privacy of all Americans. |
 | Greg Simon is a top of advisor to Al Gore for almost twenty years now. Greg has been among the Vice President’s most trusted advisers on technology issues, and one of the people whose work has enabled Al Gore to direct the nation’s attention to the almost entirely unregulated markets in information about consumers. |
 | Robert Ellis Smith is a journalist who uses his training as an attorney to report on an individual’s right to privacy. He has published Privacy Journal, a monthly newsletter, since 1974 and is the author most recently of Ben Franklin’s Web Site: Privacy and Curiosity from Plymouth Rock to the Internet. |
 | Lisa Napoli has been covering the online world since the early days of the Internet. A former columnist and reporter for the New York Times CyberTIMES, she has also been a television producer and documentary film-maker. |
 | Robert Gellman is a privacy and information consultant in Washington, D.C A Yale Law School graduate, he served for 17 years as chief counsel to the Subcommittee on Government Information in the House of Representatives. In 1996 he was appointed as amember of the Department of Health and Human Service's National Committee on Vital and Health Statistics. |
 | Evan Hendricks has served since 1981 as Editor/Publisher of the Privacy Times, a biweekly newsletter in Washington that reports on privacy and freedom of information law. He is also author of Your Right To Privacy. |
 | El St. John is an entrepreneur who established Silver Tech, Inc. in 1997 and has patented its 'Private Internet Engine', which enables groups to build secure private Internets on top of the openpublic Internet. The first application of this technology is eKidsInternet.com, worlds first private Internet network for kids that features its own browser and search engine. Prior this El founded Golden Road Presents, Inc., a television production company. |
 | Alex Fowler is the Senior Director of Policy and Advocacy for Zero-Knowledge Systems, a leading developer of Internet privacy technologies. A recognized authority on Internet policy issues, Alex is a former VP of strategic initiatives for the Electronic Frontier Foundation. |
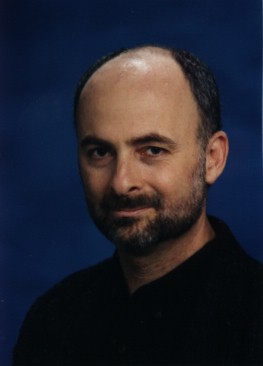 | David Brin is a scientist and author whose works of fiction have been New York Times bestsellers and whose most recent non-fiction work, The Transparent Society, has received numerous awards and honors. |